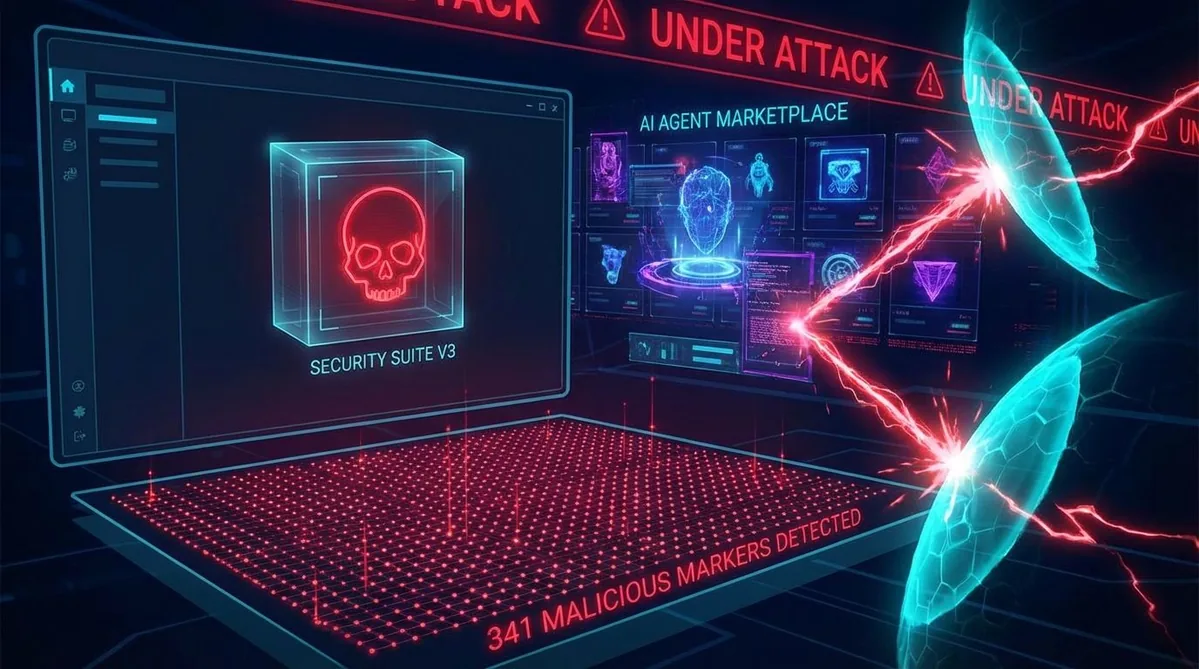
ClawHavoc: 341 Malicious Skills Found in ClawHub
Koi Security's comprehensive audit uncovers a massive supply-chain attack targeting OpenClaw users through poisoned ClawHub skills.
🦞 OpenClaw Updates
ClawHavoc: The Biggest AI Agent Supply-Chain Attack Yet
Koi Security dropped a bombshell today: their comprehensive audit of all 2,857 skills on ClawHub found 341 malicious skills, with 335 traced to a single coordinated campaign they've dubbed "ClawHavoc." This is the first large-scale supply-chain attack specifically targeting AI agent ecosystems.
The findings, covered by The Hacker News, SC Media, and eSecurity Planet, reveal that the attack exploits the trust relationship between AI bots and their users — tricking agents into installing infostealers disguised as legitimate tools.
"We found 341 malicious skills — 335 of them from what appears to be a single campaign." — Koi Security researchers
The malicious skills deploy the Atomic macOS Stealer (AMOS), targeting cryptocurrency wallets, browser credentials, and system keychain data.
This was inevitable. Any open marketplace — npm, PyPI, Chrome Web Store, now ClawHub — eventually attracts malicious actors. The key question is how the ecosystem responds. ClawHub's response (VirusTotal integration, community reporting with 3-report auto-hide) is solid. The VoltAgent curated list filtering 5,705 skills down to 3,002 trusted ones is another layer. For enterprise deployments, we recommend maintaining an approved skill allowlist and never installing skills from unverified sources.
🔒 Security Tip of the Day
Create an Approved Skills Allowlist
For any production OpenClaw deployment, maintain a curated list of approved skills. Only install skills that have been:
- Reviewed by your security team or a trusted curator (like the awesome-openclaw-skills list)
- Scanned by VirusTotal (check the ClawHub skill page)
- Verified against the Koi Security malicious skills database
- Tested in a sandbox environment before production deployment
Pro tip: Install the clawdex skill from Koi Security to get automated pre-installation scanning.
⭐ Skill of the Day: automation-workflows
🔧 automation-workflows
What it does: Helps design automation workflows across tools. Identifies repetitive tasks in your workflow, sets up triggers and actions, and teaches your agent to build workflows for you. Think Zapier, but driven by natural language.
Install: npx clawhub@latest install automation-workflows
Source: Verified on ClawHub and recommended in the Reddit best-skills thread.
Why we like it: Meta-automation — your agent learns to automate your automations. Particularly useful for identifying repetitive patterns you haven't noticed and suggesting workflow improvements.
👥 Community Highlights
The ClawHavoc disclosure triggered a massive response on the OpenClaw Discord. The community rallied around security best practices, and several experienced users published their skill-vetting workflows. The official OpenClaw team acknowledged the issue and fast-tracked the VirusTotal integration.
🌐 Ecosystem News
VPNCentral Coverage: VPNCentral's analysis provides additional context on the AMOS infostealer and how it specifically targets macOS users — a significant concern given OpenClaw's popularity among Mac developers using dedicated Mac Minis as agent hosts.
Need help with OpenClaw deployment?
SEN-X provides enterprise OpenClaw consulting — architecture, security hardening, custom skill development, and ongoing support.
Contact SEN-X →