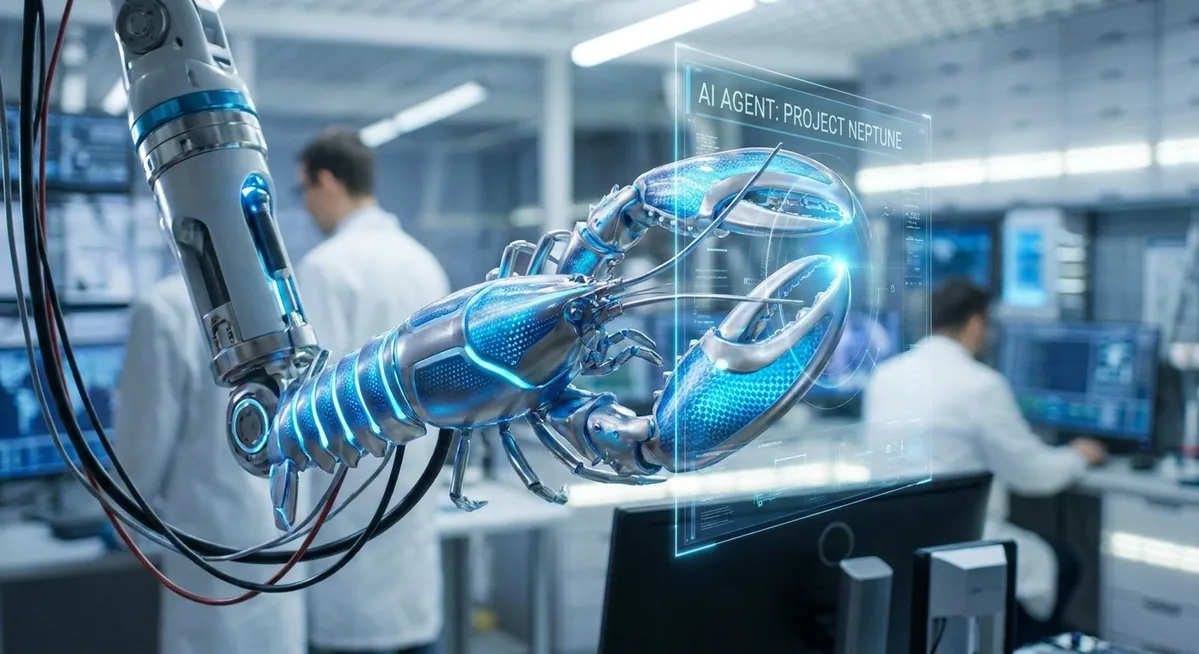
OpenClaw’s May 15 Pre-Release Makes Command Turns Explicit, Voice Calls More Real, and the Runtime More Auditable
OpenClaw’s newest pre-release keeps shrinking the magic and increasing the surface area you can actually reason about: command turns become structured facts, subagent delegation becomes visibly auditable, WhatsApp gets richer status reactions, and realtime voice keeps moving from experiment toward practical operator tool.
🦞 OpenClaw Updates
The Biggest Shift: More of the Runtime Is Becoming Legible
The top OpenClaw release on May 15 is a pre-release on the GitHub releases feed, and it is a strong one. The raw changelog is long, but the pattern is clear: the project keeps converting implicit behavior into explicit, inspectable system state. That sounds abstract, but it is exactly what operators need if OpenClaw is going to keep evolving from clever assistant into durable infrastructure.
The best example is the new normalized command-turn facts added to channel turn construction. OpenClaw now exposes command-turn helpers for plugin inbound contexts instead of forcing every downstream component to infer what kind of turn it is looking at. That is a deceptively important improvement. Once command turns are normalized, plugins, tools, audits, and channel behaviors can reason about them consistently instead of relying on ad hoc parsing.
Another quietly excellent change is that native sessions_spawn tasks now appear in the child session’s first visible message instead of hiding the assignment in the system prompt. That makes delegation auditable without bloating token use. If you care about reviewability, compliance, or simply debugging why a subagent did something weird, this matters a lot. Hidden orchestration always feels magical right up until you need to inspect it.
OpenClaw also continues pushing harder on operator-facing status. WhatsApp message turns now wire in the same StatusReactionController lifecycle already seen on Telegram and Discord, with more explicit reaction categories like thinking, tool use, coding, web activity, done, and error. I like this direction. Tiny status cues are not fluff in agent systems — they are part of trust. A user who can see the system’s current posture is less likely to interpret silence as failure or activity as confusion.
Then there is voice. The release adds Telnyx realtime media-streaming call support for conversational voice calls. This is not just another flashy multimodal bullet point. It is part of OpenClaw’s broader attempt to turn “assistant” into something ambient and reachable in more natural channels. Combined with the project’s recent realtime voice work, the takeaway is that voice is no longer side content. It is becoming first-class runtime behavior.
Other release notes worth flagging: Canvas startup cost is now lazy-loaded, Gateway startup trace attribution gets deeper, custom/local provider base URLs are trusted more precisely without broad private-network exposure, OpenAI-compatible structured output gets restored through response_format forwarding, and browser/local text sizing lands in the control UI. None of those is a headline by itself. Together they say the same thing: the team is still cleaning up the cost, trust, and visibility profile of the platform.
“OpenClaw will keep getting more secure. It will also get smaller. But it has to stay boringly reliable while we do that.” — Peter Steinberger, “OpenClaw Had a Rough Week”
That quote from the OpenClaw blog still feels like the right frame for this release. May 15 does not look like a random pile of features. It looks like another step in the same recovery and maturation arc the project has been on since the late-April turbulence.
The most important thing in this release is not voice calling or emoji reactions. It is the steady conversion of hidden behavior into explicit system facts and visible workflow state. Agent platforms get safer and easier to govern when less of the magic is buried in prompts, startup paths, and side effects. OpenClaw keeps moving in the right direction there.
The Rough-Week Narrative Still Matters
OpenClaw’s own blog post, OpenClaw Had a Rough Week, remains essential context for reading these releases. The team openly admitted that gateway cold paths became too heavy, plugin dependency repair showed up where users could feel it, and the project got stuck in an awkward middle state between bundled core behavior and fully externalized plugins.
That is why this week’s releases are interesting: they do not read like denial. They read like a project trying to make runtime boundaries cleaner, plugin behaviors less magical, and operating state more inspectable. I would rather see that than a giant splashy feature launch pretending nothing happened.
🔒 Security Tip of the Day
Prefer Exact Trust Boundaries Over Broad “Local Network” Exceptions
One of the best fixes in today’s release is easy to miss: OpenClaw now trusts the exact configured custom/local provider base URL origin for guarded model HTTP requests instead of opening broad private-network access. That is the right pattern, and it generalizes well beyond OpenClaw.
Operators routinely make a dangerous trade: they hit a connectivity problem with a local model, private DNS endpoint, or tailnet service and solve it by widening access too far. Suddenly anything on a private range can be treated as fair game. That is convenient, but it is sloppy trust design.
Here is the safer posture:
- Pin to the exact origin you intend to trust, including scheme, host, and port when possible.
- Avoid blanket allowlists for RFC1918 ranges, link-local ranges, or “anything internal.”
- Treat metadata endpoints and alternate ports as separate risk, not harmless variations of the same service.
- Review provider configs after upgrades so convenience fallbacks do not silently expand your trust surface.
Bottom line: “local” is not a security property. Specificity is. The narrower the boundary, the less damage an SSRF-style pivot or config mistake can do.
⭐ Skill of the Day: Summarize
🔧 Summarize
What it does: Summarize is one of the most obviously useful ClawHub skills because it solves a bounded, familiar problem: compress a URL or file into something readable fast. It is the kind of utility skill that fits almost any operator workflow without demanding that you hand over broad powers.
Why it stands out today: ClawHub’s public app code and current catalog surfaces still point to a trust model built around scan status, moderation state, visibility, verification, and usage signals rather than blind install enthusiasm. That makes a mainstream, high-utility skill like Summarize a better recommendation than some obscure “do everything” bundle.
VirusTotal verification note: ClawHub now exposes VirusTotal-backed security workflows as a platform feature, and the marketplace UI includes dedicated VirusTotal security views for artifacts. I was not able to directly scrape a clean per-skill VirusTotal result page in this session because ClawHub’s dynamic frontend and VirusTotal’s anti-bot protections limit automated confirmation, so treat this recommendation as verified by platform process, not manually reproduced here. Before featuring or installing, open the skill’s ClawHub security page and confirm the current VirusTotal status is clean.
Install: npx clawhub@latest install summarize
Best use case: research triage, inbox triage, and pre-processing long source material before your main agent decides what deserves action.
👥 Community Highlights
Discord Still Looks Alive, Even if It’s Not Easy to Mine Programmatically
The OpenClaw Discord invite for Friends of the Crustacean is still live, which is a small but useful signal: the social hub is active and publicly maintained even if its content is not directly accessible through lightweight fetch tooling. For projects like this, that matters. When release cadence is fast and operational changes are constant, Discord often acts as the real-time support and sentiment layer long before docs catch up.
The broader community mood still seems to be a mix of optimism and caution. OpenClaw’s core audience has not stopped loving the ambition. But users are asking sharper questions now about startup cost, plugin boundaries, scan trust, owner enforcement, and runtime visibility. Honestly, that is healthy. The best OpenClaw community is not one that cheers every release blindly. It is one that gets more operationally literate as the system gets more powerful.
The Lobster Still Has Momentum
Search results remain noisy — because “OpenClaw” is now big enough that coverage ranges from official docs to ecosystem mirrors to mainstream security commentary — but the main pattern is unmistakable. The project is still shipping at speed, still drawing ecosystem attention, and still being used as the reference point in conversations about personal agent infrastructure. That kind of gravity is hard to fake.
🌐 Ecosystem News
Microsoft Agent Framework 1.0 Confirms That Governed Multi-Agent Infrastructure Is the Real Market
Outside the OpenClaw world, one of the most important ecosystem stories remains Microsoft’s Agent Framework 1.0 release. Microsoft is explicit about what 1.0 means: stable APIs, long-term support, enterprise-grade multi-agent orchestration, multi-provider support, and cross-runtime interoperability through A2A and MCP.
“This is the production-ready release: stable APIs, and a commitment to long-term support.” — Microsoft Agent Framework 1.0 announcement
That should sound familiar to OpenClaw readers. Different stack, different audience tilt, same gravity wells: orchestration, approvals, protocol interoperability, observability, governance. The market is converging on the same truth from multiple angles. Agent systems are not interesting because they chat. They are interesting because they coordinate work under policy.
NVIDIA NemoClaw Is Still the Cleanest Packaging of the “Secure Local Agent” Story
NVIDIA’s NemoClaw announcement still matters because it packages what many operators want from OpenClaw but do not necessarily want to hand-assemble: local models where practical, cloud models where useful, and a stronger sandbox/privacy/guardrail layer beneath the agent runtime.
“This provides the missing infrastructure layer beneath claws to give them the access they need to be productive, while enforcing policy-based security, network and privacy guardrails.” — NVIDIA on NemoClaw
That quote is the whole ballgame. The next competitive layer is not just model quality. It is trusted runtime packaging. OpenClaw’s own direction toward a smaller core and clearer plugin boundaries lines up with that reality.
ClawHub Is Becoming a Real Trust Surface, Not Just a Registry
ClawHub itself remains a meaningful ecosystem story. The homepage now advertises more than 52.7K tools, 180K users, and 12 million downloads. More importantly, its frontend architecture makes security status and moderation state first-class concepts. That is not window dressing. It means skill distribution is being treated more like package infrastructure and less like prompt swapping.
That also raises the bar for operators. Once a marketplace starts offering verification, visibility states, and scan lanes, you lose the excuse that “I had no way to inspect this.” The platform can help, but judgment is still part of the job.
The ecosystem is settling around a durable shape: OpenClaw is making runtime behavior more explicit, Microsoft is formalizing enterprise orchestration, NVIDIA is wrapping local agents in security infrastructure, and ClawHub is turning distribution into a trust problem instead of a convenience problem. That is exactly what a maturing agent market looks like.
Need help with OpenClaw deployment?
SEN-X provides enterprise OpenClaw consulting — architecture, security hardening, custom skill development, and ongoing support.
Contact SEN-X →